[ad_1]
Business Continuity Management / Disaster Recovery
,
Critical Infrastructure Security
,
Cybercrime
An ICS-capable Malware and Several Disk Wipers Stopped Before Deployment
Targeted attacks on a Ukrainian energy facility have been confirmed by the Computer Emergency Response Team of Ukraine (CERT-UA). In a joint operation carried out by the Ukrainian CERT with security companies Microsoft and firm ESET, it was found that an ICS-capable malware and several regular disk wipers for Windows, Linux, and Solaris operating systems were used in the attack.
See Also: Third Party Risk: Lessons on Log4j
CERT-UA says that it has averted the execution of these malwares that were scheduled to trigger at very specific times on the evening of April 8, and has prevented damage so far.
In a press briefing held by the Ukrainian government, Farid Safarov, Deputy Minister of Energy for Digital Development, Digital Transformation and Digitization, says that the attack was targeted at a single private energy company with operations at a couple of locations, and had the attack been successfully executed, it would have impacted two million civilians in the region where the energy company supplies electricity.
Safarov also confirmed that attackers successfully infiltrated the facility’s management system, but were then detected before their payload was deployed and the system was shut down, thus preventing damage to other systems.
Victor Zhora, deputy head of the State Service of Special Communications and Information Protection of Ukraine, adds, “We were aware that the energy sector has been on the radar [of threat actors] for quite some time now and that critical infrastructure can be targeted. But we have learnt from the previous attacks and were better prepared and thus could prevent this particular attack.”
Zhora also noted that since the beginning of Russia’s invasion, just over a month and a half ago, Ukraine has recorded three times as many attacks as compared to the entire previous year. The main target in these attacks has been critical infrastructure, but this was the most “serious” and “sophisticated” attack of all, Zhora says.
Without confirming an exact date, Zhora says, “We received information of a possible compromise of an energy facility and a subsequent malware being infected in its system from our [unnamed] international partners, which was then forwarded to the energy department that in turn confirmed the presence of the malware. Based on this, with the help of our partners we remediated and prevented the attack just in time before its implementation.”
Which Malware Was Used?
The Sandworm group that is known to have targeted Ukraine’s power grid back in December 2016 using Industroyer malware has, according to ESET, used a new version of the same malware (Industroyer2) in the current attack. “We assess with high confidence that the attackers used a new version of the Industroyer malware, which was used in 2016 to cut power in Ukraine,” ESET says.
In addition to Industroyer2, Sandworm also used several other malware families including CaddyWiper, ORCSHRED, SOLOSHRED and AWFULSHRED, where each has a different function and is used to target different parts of the industrial control systems, says CERT-UA.
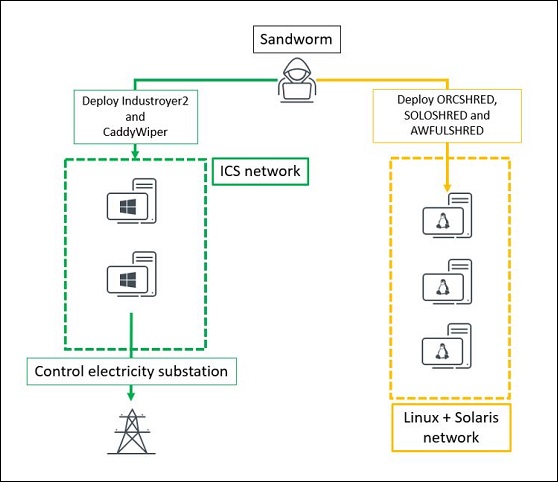
The objective of using different malware programs, as suggested by CERT-UA, was to target different infrastructural elements as follows:
- Industroyer2: To target high-voltage electrical substations.
- Caddywiper destructor: To target computer systems running the Windows operating system including user computers, servers, as well as automated workstations called automated control system of technological processes – or ACS TP.
- ORCSHRED, SOLOSHRED, AWFULSHRED: To target server equipment running on Linux and Solaris operating systems.
Apart from these specific activities, these malware are also used for reconnaissance of active network equipment.
Scheduled Timeline
CERT-UA says that two waves of attacks were designed to target the energy facility. The first was the initial compromise that took place in February 2022 and the second was supposed to hit on the evening of April 8 at around 4PM local time [16:10 UTC].
When asked about the significance of the timing scheduled for the attack, Zhora says it could have well been two reasons: support the Russian attacks in Eastern Ukraine where larger regrouping of military has been seen, and second, it is a time when commuters return home.
ESET first knew about the CaddyWiper malware on March 14, when it was deployed against a Ukrainian bank. Since then it started monitoring the activities of the associated threat actor.
ESET researchers helping CERT-UA decoding the threat summarize the chain of events related to Sandworm as follows:
- March 14: Deployment of CaddyWiper against a Ukrainian bank;
- April 1: Deployment of CaddyWiper against a Ukrainian government entity;
- April 8 [14:58 UTC]: Deployment of CaddyWiper on some Windows machines and Linux and Solaris destructive malware at the energy provider;
- April 8 [15:02:22 UTC]: Sandworm operator creates the scheduled task to launch Industroyer2;
- April 8 [16:10 UTC]: Scheduled execution of Industroyer2 to cut power in an Ukrainian region;
- April 08 [16:20 UTC]: Scheduled execution of CaddyWiper on the same machine to erase Industroyer2 traces.
Analysis of the Big Two
Industroyer2
“Industroyer2 was deployed as a single Windows executable named 108_100.exe and executed using a scheduled task on 2022-04-08 at 16:10:00 UTC. It was compiled on 2022-03-23, according to the PE timestamp, suggesting that attackers had planned their attack for more than two weeks,” ESET researchers say.
The malware only implements the IEC-104 (aka IEC 60870-5-104) protocol to communicate with industrial equipment, which includes protection relays used in electrical substations. “This is a slight change from the 2016 Industroyer that is a fully-modular platform with payloads for multiple ICS protocols. However, Industroyer2 shares number of code similarities with the payload 104.dll of Industroyer. We assess with high confidence that the new variant was built using the same source code,” ESET researchers say.
CaddyWiper
As a follow-up to Industroyer2 in the ICS network, the Sandworm group deployed a new version of the CaddyWiper malware as well. “We believe it was intended to slow down the recovery process and prevent operators of the energy company from regaining control of the ICS consoles. It was also deployed on the machine where Industroyer2 was executed, likely to cover their traces,” ESET researchers note.
The first version of CaddyWiper was deployed via Group Policy Object (GPO), which ESET researchers say, indicates that the attackers had prior control of the target’s network. “The POWERGAP PowerShell script was used to add a Group Policy that downloads file destructor components from a domain controller and creates a scheduled task on a computer,” CERT-UA notes.
The main purpose of using this wiper is that it erases data and partition information from the attached drives, making the system inoperable and unrecoverable, the ESET researchers explain.
Security Industry Lauds the Effort
John Hultquist, VP of intelligence analysis at Mandiant, tells Information Security Media Group that “Sandworm is an apex predator, capable of serious operations, but they aren’t infallible. The best part of this story is the work by Ukraine CERT and ESET to stop these attacks, which would have probably only worsened Ukrainian suffering. It’s increasingly clear that one of the reasons attacks in Ukraine have been moderated is because defenders there are very aggressive and very good at confronting Russian actors.”
Ciaran Martin, former founding head of the NCSC, in a tweet, also congratulated the CERT-UA and ESET for thwarting these attempts from Russia and for showing “great cyber defensive work.” But he added that “We can’t draw sweeping, permanent conclusions about what this tells us about cyber in war always and everywhere in the future. This experience should however give us a more realistic perspective about what cyber capabilities can and can’t do.”
[ad_2]
Source link
